Unleashing the Power of Identity & Access Management: A Comprehensive Guide

In today’s digital age, security threats are more rampant than ever before. Organizations of all sizes are under constant siege from cyber criminals, and protecting sensitive information has become a top priority. That is why Identity and Access Management (IAM) has become a critical component of modern cybersecurity. IAM is the process of managing digital identities and controlling who has access to what information. It is a comprehensive security solution that helps organizations protect their assets, both physical and digital.
However, implementing IAM can be a complex and daunting task. Especially for businesses that are still in the early stages of digital transformation. There are many different components to consider, such as authentication mechanisms, access control policies, provisioning and deprovisioning processes, and so on. But don’t worry, the comprehensive guide to IAM will help you unleash its power and achieve a more secure IT environment.
Harness the Potential of IAM
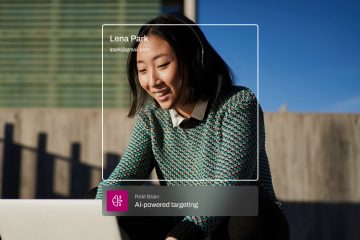
Are you ready to unleash the full potential of your organization’s security system? Look no further than helloid identity & access management, the ultimate solution for harnessing the power of IAM. With helloid, you can take control of your digital universe and ensure maximum security for your sensitive data. Whether you’re looking to streamline access to critical resources or manage the identities of thousands of users, helloid is the only tool you need. So why wait? Unlock the power of IAM today with helloid and take your security to the next level!
Discover New Ways to Secure Your Data
Helloid identity & access management presents an exciting opportunity to discover new ways to secure your data. With everything going digital, the amount of sensitive data being shared and stored online is staggering. And while there are existing procedures for data security, they can quickly become outdated and leave your organization vulnerable to cyber threats. It’s time to take a proactive approach to securing your data by embracing innovative technology like helloid. This cutting-edge identity and access management solution offers features like multi-factor authentication, password management, and real-time monitoring, all of which combine to provide robust security for your organization’s data.
Transform Access Controls with Identity Management
Are you tired of managing multiple access controls for different applications, devices, and users across your organization? Look no further than helloid Identity & Access Management, the ultimate solution for streamlining access controls and enhancing security. With helloid, you can transform your access controls by centralizing your identity management processes. This means you can drastically reduce the time and effort it takes to grant or revoke access to users, and you’ll have more control over who has access to what data.