Keeping Your Data Safe As A Digital Business

Owning a business that operates almost entirely online comes with advantages. Digital marketing companies have a global reach, and virtual infrastructure is inexpensive. That said, digital operations present a unique set of security challenges. Here are several steps entrepreneurs can take to handle cybercrime and keep their business from becoming a statistic.
Prioritize Cloud-Based Security
Using cloud-based services is nearly inevitable for modern businesses. Decentralized data storage and computing offer mobility and scalability. Most cloud providers do an excellent job of securing their facilities. Tools like data center infrastructure management (DCIM) systems enable effective crisis management. That said, security measures vary widely by company. Some providers take steps that others don’t, so be discerning when choosing a provider.
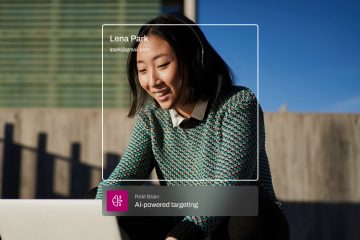
Beware Social Media Scams
Social media pages are a critical touchpoint between digital companies and their customers. Statista found that 92.1% of companies employing over 100 people used social media in marketing. Doing so can expose small businesses to whole new markets. It also exposes them to new threats. Friend request scams are indicative of something worse. Anyone can pose as your business or another business and use that appearance of legitimacy to con you out of personal (or client) information. Learning to see the difference between legitimacy and the appearance of legitimacy on social media is essential.
Get Everyone Educated
Spreading that knowledge is equally crucial. A recent study by security company Tessian revealed a startling fact. 85% of all data breaches are caused in part by human error. Often, the mistake takes the form of entering data on a phony website or clicking a spurious link. In other cases, a technical mishap is at fault. Either way, having a training regimen in place is the solution. Since nearly every employee has access to the network, instill respect for proper internet and phone use protocols in everyone.
Enforce Better Authentication Protocols
In other words, it’s time to get serious about passwords. Choosing weak passwords plays an outsize role in the aforementioned human error incidents. A common mistake is choosing a password that’s too short or not random enough. According to science, strong passwords should be at least 12 characters long and consist of randomized characters. Another typical error is the overuse of the same password. Never use the same password to access multiple sites. Don’t write the password down if you can help it. Treat it like you would any other personal information.
Utilize Firewalls
Firewall systems are an underutilized yet vital facet of cybersecurity. Not everyone has them because not everyone needs them. Businesses that operate in the digital world likely need them. The reason is simple: email. Companies engaged in digital marketing routinely deal with high email traffic. Email is a common vector for malware attacks, including ransomware. Links loaded with malicious software can enter your network quickly. Firewalls flag suspicious emails and filter them as they enter your network. It’s one more layer of defense that bears consideration.
Incorporate Strong Endpoint Security
Many, if not most, companies incorporate a vast array of devices. Remote work exacerbates the problem because people might be working from unsecured WiFi. The quality of their antivirus software likely also varies. The concept of endpoint security revolves around standardization and compliance.
Ideally, every user endpoint on your network should adhere to the same security standards. Adhering to standards means installing similar (and high) quality antivirus software. Those standards should also include basic usage protocols like not accessing risky sites or downloading potentially harmful files. Endpoint security can benefit from adopting zero-trust security architecture. Zero-trust means insisting on rigorous authentication from all new users on a network. These measures serve to mitigate risk so you can focus on growth.
The internet is a frontier laden with opportunity. Minimizing the dangers of that frontier takes awareness and knowledge. These tips are just the beginning. Keep up to date on emerging threats and their countermeasures to stay a step ahead of cybercriminals.